CIEMNO-SZARE SPODNIE JEANSOWE TYPU PUSH UP | NOWOŚCI WYPRZEDAŻ % KOLEKCJA \ Spodnie \ Spodnie PUSH UP KOLEKCJA \ Jeansy \ Jeansy PUSH UP KOLEKCJA \ Jeansy \ Jeansy skinny KOLEKCJA \
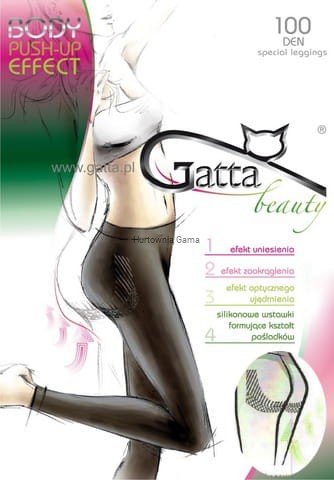
Legginsy Gatta wyszczuplające Body Push Up Effect 100 den Sklep internetowy GAMA - rajstopy,skarpety, bielizna damska, męska i dziecięca,szorty kąpielowe ,spodenki kąpielowe w Białymstoku

Melodia na wysoki wzrost Sexy legginsy typu Push Up ciemnoniebieski zamek latać Super wygodne ołówkowe legginsy dla legginsy damskie Fitness mujer| Legginsy| - AliExpress

Legginsy Bezszwowe Grey Melange Shape (Push Up) | Legginsy bezszwowe \ Legginsy z wysoką kompresją - bezszwowe Odzież \ Legginsy bezszwowe \ Legginsy z wysoką kompresją - bezszwowe | Boco Wear

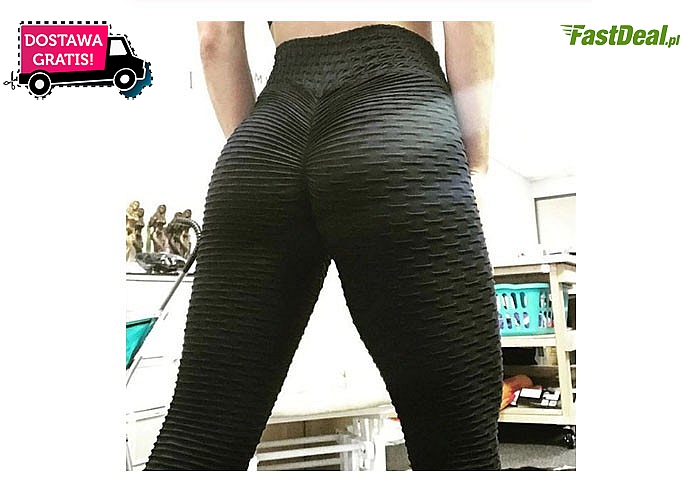
Ruuhee Seamless Push Up Leggings Scrunch Butt Women's Fitness Workout Clothing High Waist Bum Sport Gym Solid Yoga Pants - Yoga Pants - AliExpress

Legginsy Bezszwowe Grey Melange Shape (Push Up) | Legginsy bezszwowe \ Legginsy z wysoką kompresją - bezszwowe Odzież \ Legginsy bezszwowe \ Legginsy z wysoką kompresją - bezszwowe | Boco Wear